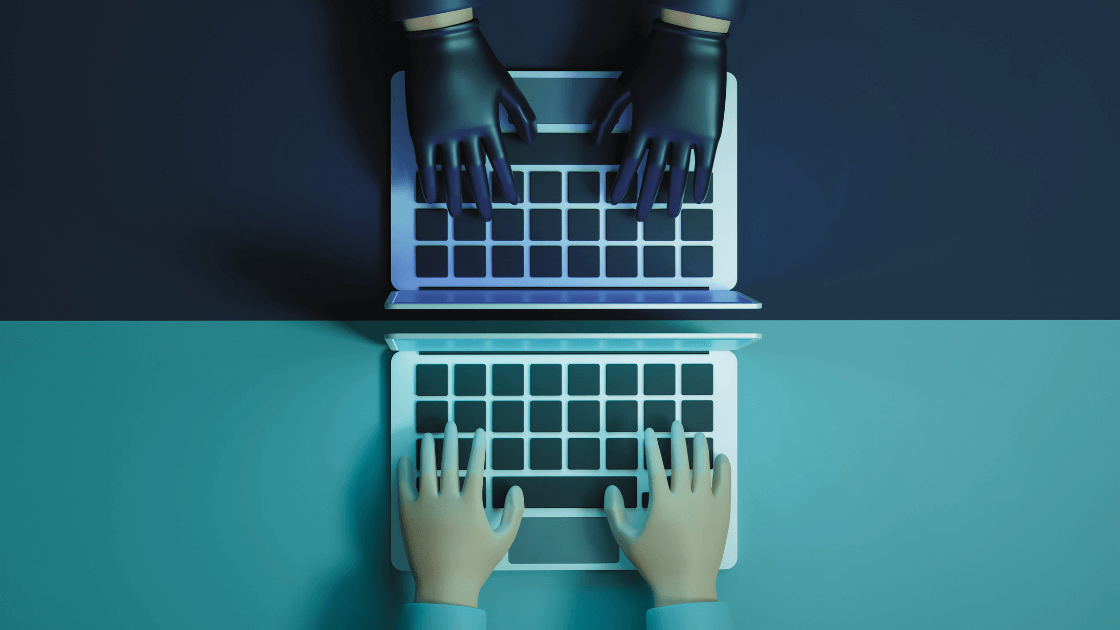
A Trojan Horse, or, simply, a trojan, is a kind of malware that hides within computer programs and is designed to damage, disrupt, steal, or inflict some other harmful action on your data or network. The infected code is meant to trick you into loading and executing the malware on your device. Unlike viruses, trojans do not replicate and infect other files, nor do they make copies of themselves like worms. They might work properly alongside existing programs, going totally unnoticed by the user. They may sit quietly in your computer, collecting information or setting up holes in your security, or they may just take over your computer and lock you out. Some common actions trojans take are creating backdoors, which means making changes to your security system so the hacker can get in and disrupt your network. At other times, they are designed to be spyware, collecting information like credit card numbers, passwords, or social security numbers. A trojan also can be camouflaged as an antivirus system. If your computer is infected, a message will pop up saying that viruses have been detected on your computer and they can be removed for a fee. In this case, the message, itself, is the virus! Trojans are, by design, misleading and formulated to trick you into using them. Follow these guidelines to protect yourself from these devious threats.
- Run periodic diagnostic scans on your systems.
- Update your software when available.
- Be cautious when opening emails from unknown sources.
- Back up files regularly.
- Don’t click on pop-up windows.
- Don’t visit unsafe websites.
- Avoid opening unsolicited emails from senders you don’t know.
- Don’t open a link in an email unless you know exactly what it is.