 Forget Ransomware – Data Extortion Is The New Cybersecurity Nightmare For Businesses Like Yours
Forget Ransomware – Data Extortion Is The New Cybersecurity Nightmare For Businesses Like Yours
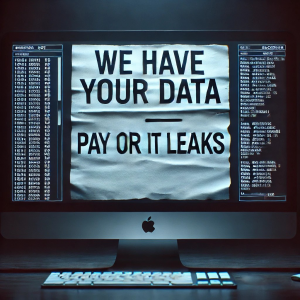
If you thought ransomware was your biggest cybersecurity concern, it’s time to think again. Hackers have evolved their tactics, and they’re now skipping encryption altogether. Instead, they’re stealing your sensitive business data and threatening to leak it publicly unless you pay a ransom.
This fast-growing threat is called data extortion, and it’s even more ruthless than traditional ransomware attacks.
Here’s how it works:
Hackers quietly infiltrate your network, steal critical files, and then demand payment to prevent public exposure. No more waiting for decryption keys or restoring systems — just the terrifying risk of your private business data, client records, or financial information being published on the dark web for the world to see.
According to Cyberint, more than 5,400 data extortion attacks were reported globally in 2024, an 11% increase from the previous year. And the trend isn’t slowing down.
Why Data Extortion Is Outpacing Traditional Ransomware
Data extortion skips the step of encrypting your files, making it faster, stealthier, and even more profitable for cybercriminals. Here’s how these attacks unfold:
-
Data Theft: Hackers infiltrate your systems and extract sensitive information — client lists, payroll details, intellectual property, vendor contracts, and more.
-
Extortion Demand: Rather than locking you out of your data, they threaten to leak it publicly if you refuse to pay.
-
No Decryption Required: Without needing to encrypt data, they can avoid detection from traditional ransomware defenses.
This new method puts your reputation, regulatory compliance, and business continuity at immediate risk.
The Real Dangers of Data Extortion for Businesses
Data extortion does more than disrupt operations — it hits where it hurts most: your relationships, your reputation, and your bottom line.
1. Reputational Damage & Loss of Trust
Leaked client or employee data can irreparably harm your reputation. Trust, once lost, is nearly impossible to regain — especially in industries like legal, healthcare, or finance where confidentiality is critical.
2. Regulatory & Compliance Violations
Exposure of sensitive data triggers hefty penalties under regulations like GDPR, HIPAA, and PCI DSS. Regulatory scrutiny and fines can devastate small to mid-sized businesses.
3. Costly Legal Consequences
Data breaches often lead to lawsuits from customers, employees, or partners whose information was compromised.
4. Endless Extortion Cycles
Even if you pay the ransom, there’s no guarantee the attackers won’t come back. Hackers often keep copies of your data for future leverage.
Why Are Hackers Shifting to Data Extortion?
Because it works — and it works fast.
-
Quicker Paydays: Encryption takes time, but data theft is swift and silent.
-
Harder to Detect: Traditional antivirus and endpoint tools often miss data exfiltration masked as normal network traffic.
-
Stronger Emotional Leverage: The fear of public exposure pressures business owners into paying up.
Traditional Cybersecurity Defenses Are No Longer Enough
If your defenses are limited to firewalls and antivirus software, you’re dangerously exposed. Data extortion attacks bypass these basic protections by:
-
Harvesting login credentials with info stealers.
-
Exploiting vulnerabilities in cloud storage.
-
Hiding stolen data transfers as legitimate network activity.
Hackers are also using AI-powered tools to automate attacks, making them faster and harder to detect.
How To Protect Your Business From Data Extortion
To defend against data extortion, you need to go beyond basic cybersecurity. Here’s how to build a stronger defense:
1. Adopt a Zero Trust Security Model
-
Assume every device and user is a potential threat.
-
Enforce strict identity and access management (IAM).
-
Use multifactor authentication (MFA) across your organization.
-
Continuously monitor all network activity.
2. Invest in Advanced Threat Detection and Data Loss Prevention (DLP)
-
Use AI-driven monitoring tools to detect suspicious behavior.
-
Stop data exfiltration in real time.
-
Monitor your cloud environments for unauthorized access.
3. Encrypt Sensitive Data
-
Encrypt data at rest and in transit to neutralize theft.
-
Use secure protocols for data sharing and communication.
4. Maintain Reliable Backups and Disaster Recovery
-
While backups won’t stop data theft, they’ll help restore operations faster.
-
Use offline backups to prevent ransomware destruction.
-
Regularly test your backups to ensure reliability.
5. Train Your Team
-
Educate employees on recognizing phishing and social engineering attacks.
-
Establish clear protocols for reporting suspicious activity.
-
Foster a culture of cybersecurity awareness.
Don’t Wait Until It’s Too Late
Data extortion isn’t a future threat — it’s happening right now to businesses just like yours. And as these attacks become more sophisticated, the time to act is now.
Let’s make sure your business is ready.
Schedule your FREE Network Assessment today.
Our cybersecurity specialists will analyze your current defenses, identify risks, and build a proactive strategy to keep your sensitive data protected.
Call us at 440-322-4537 or click here to schedule your free assessment now!
Cyberthreats are evolving. Isn’t it time your cybersecurity strategy evolved too?






