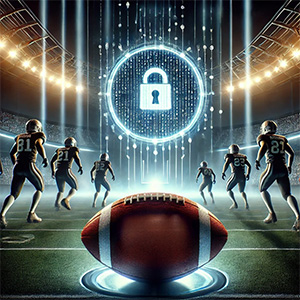
It’s game time – and while the biggest teams are gearing up for football’s biggest day, cybercriminals are busy preparing their playbook for 2025. Just like a championship game, defending your business against hackers requires strategy, teamwork, and preparation.
As a business owner, you’re already juggling compliance, cybersecurity, and operational efficiency. The last thing you need is a cyberattack disrupting your workflow. Are you ready to tackle this year’s biggest cybersecurity threats? Here’s what experts predict for 2025 and how your business can stay ahead.
This Year’s Cybersecurity MVPs (Most Vicious Perpetrators)
1. AI-Powered Phishing Plays
Cybercriminals are using artificial intelligence to craft highly personalized and convincing phishing emails that can deceive even the most cautious employees. These emails often mimic trusted brands, vendors, or even internal colleagues.
Your Defense:
– Train employees to recognize phishing attempts.
– Implement advanced email filtering tools to detect and block suspicious messages.
– Use multifactor authentication (MFA) to add an extra layer of security to accounts.
2. Ransomware Blitz
Ransomware continues to be one of the biggest threats to businesses of all sizes. Hackers aren’t just encrypting data anymore—they’re threatening to leak sensitive company information unless ransoms are paid.
Your Defense:
– Regularly back up data and store backups off-site.
– Ensure systems and software are updated with the latest security patches.
– Deploy advanced endpoint protection to detect and block ransomware before it takes hold.
3. Supply Chain Sneak Attacks
Hackers are increasingly targeting small and midsize businesses as entry points into larger supply chains. A breach in your network could put your vendors and clients at risk.
Your Defense:
– Vet vendors to ensure they follow strict cybersecurity protocols.
– Segment your network to limit access points for attackers.
– Implement a zero-trust security model, verifying every user and device.
4. Deepfake Decoys
Deepfake technology is being weaponized to impersonate executives, tricking employees into transferring funds or sharing sensitive information.
Your Defense:
– Verify any unusual requests via a second communication method (e.g., a direct phone call).
– Educate your team about the risks and signs of deepfake scams.
– Limit the sharing of sensitive company information online that could be used to create convincing fakes.
5. Internet of Things (IoT) Fumbles
Smart devices such as printers, cameras, and thermostats often have weak security settings, making them easy entry points for hackers.
Your Defense:
– Change default passwords on all IoT devices.
– Regularly update device firmware to patch vulnerabilities.
– Isolate IoT devices on a separate network to minimize risk.
Your Game Plan for 2025
Winning against cybercriminals requires more than just strong defenses—it takes a proactive game plan. Here’s how your business can stay ahead:
Draft Your Team: Partner with a trusted IT provider like Iler Networking & Computing to proactively monitor and protect your systems.
Study the Playbook: Stay informed about emerging threats and best practices to counter them.
Run Practice Drills: Regularly test your backups and conduct cybersecurity training with your employees.
Get Your Free Cybersecurity Game Plan
Ready to strengthen your cybersecurity strategy? Schedule a FREE Network Assessment today. We’ll identify vulnerabilities, provide actionable solutions, and ensure your business is prepared to beat the hackers this year.
Click here to schedule your FREE Network Assessment now or call 440-322-4537 to speak with an expert.
Don’t let cybercriminals take the lead. With the right strategy and team, your business can stay secure and thrive in 2025.